Imagine a piece of software a bit like a house. Overall, it might be very solid and able to perform the job that is asked of it, but there are almost certainly some slight flaws that could be fixed.
Maybe they are cosmetic: not really causing any harm other than minor irritation every now and then. In other cases, they could be more serious. If your front door won’t lock, or one of the ground floor windows could be easily pushed open, it becomes more than an annoyance — it turns into a liability.
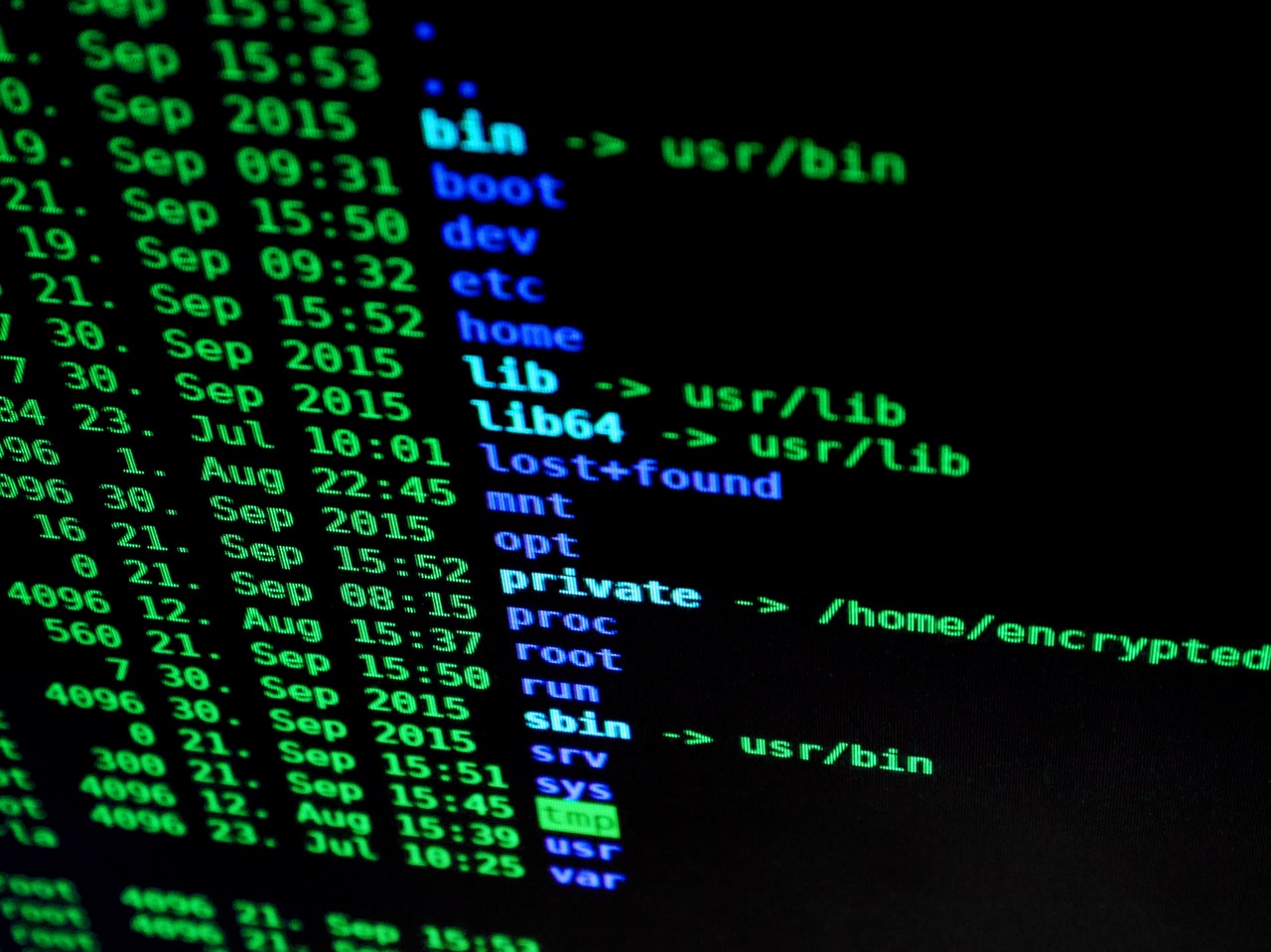
No piece of software is 100 percent perfect. Virtually every piece of code written has bugs. The larger and more ambitious the software, the more bugs you can expect.
But while some of these will just represent tiny nuisances to the user, others represent vulnerabilities by which a bad actor could exploit the software weaknesses to cause damage. In short, it is the difference between a program not working the way that it should, and a glaring vulnerability that can be used for malicious purposes.
This is where application security comes into the picture.
The right patch
 Many vulnerabilities can be solved by using the right patch. A patch refers to changes made by a developer to their software, frequently as a way of protecting against security vulnerabilities and assorted other bugs that have been discovered.
Many vulnerabilities can be solved by using the right patch. A patch refers to changes made by a developer to their software, frequently as a way of protecting against security vulnerabilities and assorted other bugs that have been discovered.
While there is such a thing as zero-day attacks, referring to vulnerabilities that have not been patched by developers, in lots of cases developers (at least, the diligent ones) act very quickly when a vulnerability is disclosed and issue a patch to solve the problem.
Unfortunately, what solves the problem technically doesn’t necessarily translate to a solution for many users. The reason for this is that, in order for a patch to be useful, users must download and install it. Those who fail to do so are not protected. Returning once more to the house analogy, it is a bit like knowing that your front door won’t lock properly — but failing to do anything about it.
This might sound (and maybe) reckless on the part of businesses and anyone else at risk of a cyberattack that exploits a software vulnerability. However, it is difficult to totally blame them.
Every year there are thousands of vulnerabilities reported to organizations such as the National Institute of Standards and Technology (NIST), which keeps track of them. Of the 17,000+ vulnerabilities reported to NIST in 2020, upward of 4,000 were classified as a high priority.
Relying on more apps than ever
Modern businesses may rely on anywhere from a few dozen to more than 200 software applications. Keeping all of these updated, and staying attuned to the threats they face, is virtually a full-time job (or more) in itself. Many businesses do not have the resources to do this and may miss out on crucial updates as a result.
Security teams have other priorities, which can result in spotty adoption of patches. Lots of teams will have a sizable backlog of patches to download, install, and test to ensure that they are working correctly.
What is needed is effective vulnerability prioritization. As noted above, vulnerabilities are different (and more dangerous) than regular software bugs. But not every vulnerability is the same. Some are easier or harder to exploit than others. Good vulnerability management is therefore about not just finding and patching vulnerabilities, but also triaging them to make sure that the most critical ones are addressed first.
This is where lists such as those published by NIST can play a valuable role, by highlighting the most critical vulnerabilities. By paying special attention to these reports, companies and organizations can make sure that they install the patches most likely to cause immediate harm while reserving the less crucial ones for later.
Not a long-term solution
 Patching is not a scalable, long-term strategy, however.
Patching is not a scalable, long-term strategy, however.
Yes, patches are a good idea to install as quickly as possible (software updates also frequently include new features that go beyond simply blocking vulnerabilities.) But there are other ways of more immediately blocking the exploitation of vulnerable apps.
Tools like Runtime Application Self-Protection (RASP) and Web Application Firewalls (WAFs) can work to block potential threats by identifying and blocking malicious inputs and request payloads.
Virtual patching is also a game-changer in this regard. Instead of having to wait for, and install, an official patch, virtual patching takes the form of a series of rules that put a block of malicious behavior that could otherwise inflict damage.
By using cybersecurity tools such as this, you can safeguard against attacks that might otherwise cause considerable damage. Doing so is an essential move for any business or organization that wants to be proactive about its defenses. It is hard to think of a better investment of resources.

The Ideas Plus Business Editorial team is responsible for this post. For collaborations and partnership requests, kindly send an email to the Editorial Team at ideasplusbusiness[at]gmail[dot]com for the terms and conditions. You can also follow IdeasPlusBusiness.com on Twitter here and like our page on Facebook here.
